Shipa has announced the general availability of Shipa 1.2, which adds several key integrations to make the framework simple to use with other solutions popular with application developers and DevOps teams.
Key new features include: Network Policies Map, Integration with Istio – including canary rollouts, Vault integration and Integration with Private Registries – including JFrog.
Shipa users can now use their existing Istio ingress controller for their deployed applications. This includes leveraging the open source service mesh for traffic routing rules, including canary rollouts based on traffic-percentage splits.
Istio-generated service metrics, as well as CNAME and HTTPS certificate management, are also now available and included in Shipa’s network mapping capabilities as part of this integration.
Shipa users also can inject secrets from their HashiCorp Vault into their Kubernetes applications deployed using Shipa. The framework enables users to pass all requisite vault annotations through shipa.yaml; annotations are then used by Kubernetes Vault sidecar to inject secrets into users’ applications.
Shipa now provides the ability to deploy applications with Docker images stored in private registries. This feature uses an image URL, Docker username, and password/access token to gain access. Shipa is now offering full support for JFrog Artifactory, Docker Hub, Amazon ECR, Azure Container Registry, Google GCR, Nexus repository, and more.
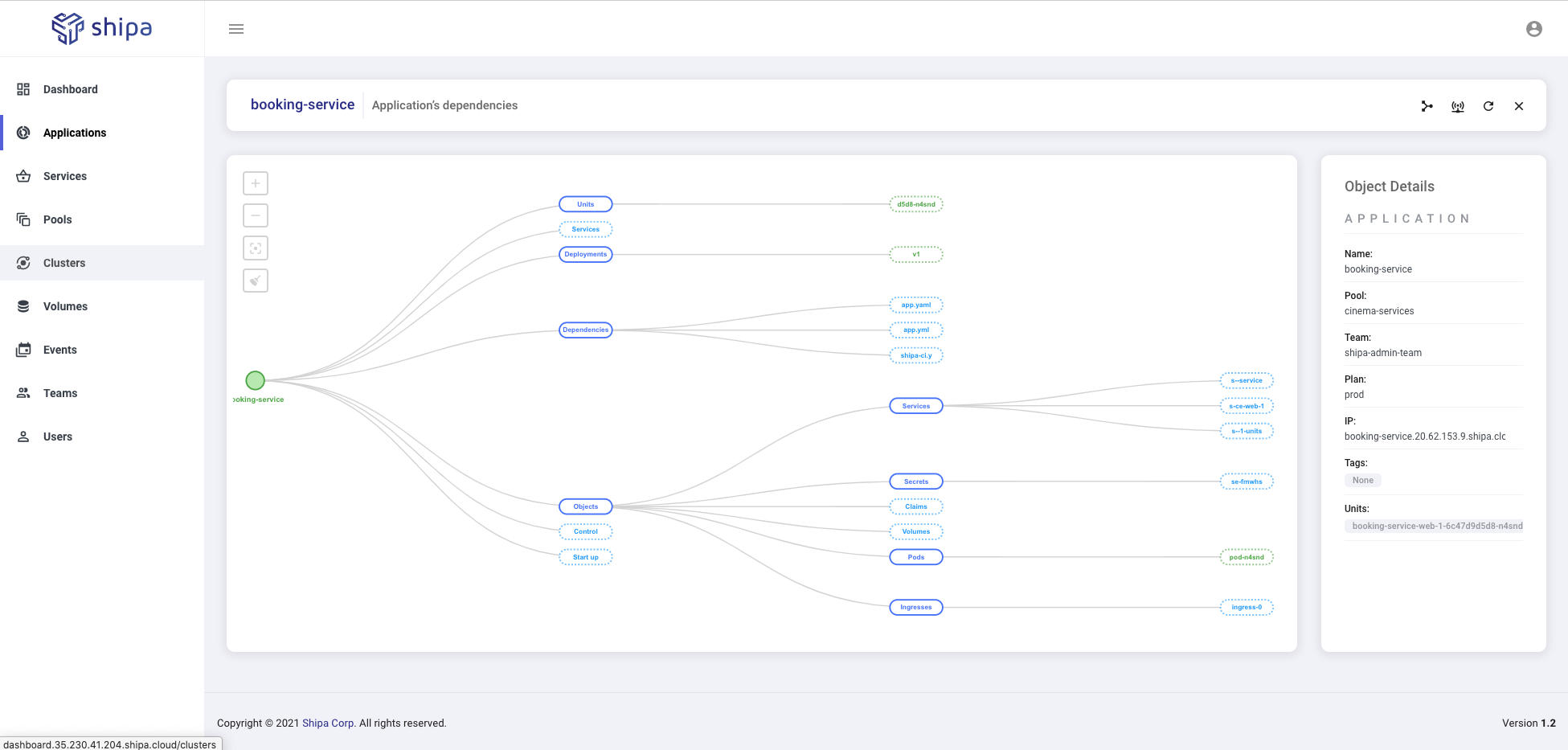
Additionally, Shipa now empowers its users with a visual translation of standard Kubernetes network policies, representing the simple abstraction level that Shipa provides when restricting or allowing traffic flow between applications and services.
Shipa 1.2 also expands framework flexibility to better meet users in the cloud environments they are working in. The new release expands Shipa’s multi-cloud functionality to include AKS, EKS, OKE, GKE, IKS, and OpenShift. Shipa has also made improvements to its multi-tenancy model.